Difference between revisions of "Security-SIG"
Nickthetait (talk | contribs) m (Update a URL) |
GuanYu, lin (talk | contribs) (→Leadership) |
||
| Line 10: | Line 10: | ||
=== Leadership === | === Leadership === | ||
| − | The security SIG has no formal leadership, instead it has chairs who arrange meetings and organise votes.. The current | + | The security SIG has no formal leadership, instead it has chairs who arrange meetings and organise votes.. The current chair is Gage Hugo (AT&T). |
Chair duty rotates each month. | Chair duty rotates each month. | ||
Revision as of 11:42, 8 September 2019
Security issues, tooling, innovations and education within OpenStack are the responsibility of the Security SIG. The Security SIG is a horizontal effort within OpenStack that is comprised of what was previously referred to as the OpenStack Security Project. The Security SIG undertakes both technical and governance activities within OpenStack, aiming to provide guidance, information and code that enhances the overall security of the OpenStack ecosystem.
Contents
Organization and Contribution
The Security SIG is built up primarily of two groups of people; those who write OpenStack code and those who try to secure OpenStack clouds! We have contributors from over 30 different companies involved in OpenStack. If you're interested in helping to make OpenStack more secure, either through writing better code, cross project collaboration, writing documentation or inventing cool new features and tooling - we want to hear from you!
Leadership
The security SIG has no formal leadership, instead it has chairs who arrange meetings and organise votes.. The current chair is Gage Hugo (AT&T).
Chair duty rotates each month.
IRC
The security SIG has an IRC room (#openstack-security) on irc.freenode.net that's used for general communications, chat and the occasional user query. The security SIG meets weekly to discuss progress on individual activities. We encourage new contributors to say hello during our weekly meetings.
- Weekly meeting IRC information
- Weekly meeting logs
- Logs from the #openstack-security room
- IRC WebChat Client
Contribution
The process of becoming a member of the group is described on the OSSG Launchpad page. At the moment of writing, there is no defined "procedure" to get involved into the OSSG and a suggested set of steps follows. Each described steps might or not be relevant depending on the individual member's background and familiarity with the OpenStack project.
Some steps to get started are:
- Read the OpenStack documentation and understand the most common deployment scenarios.
- Go through the OpenStack installation guide and create a deployment (either a native one or in a virtualized environment), in order to get a basic understanding of the interaction of the different OpenStack services. Some installation scripts such as Devstack and Packstack are readily available. However, you should not underestimate the educational benefits of spending some quality time to install OpenStack manually.
- Read the newly released OpenStack security guide in order to dive into the security aspects of setting up and running an OpenStack deployment.
- Getting acquainted to some degree with the rest of the OpenStack manuals is highly encouraged.
- The next step is to choose one of the OpenStack components in order to become closely familiarized with it and eventually be able to use the combined expertise of the OSSG in order to make thoughtful contributions to the component (code reviews, direct code contribution, architectural aspects) and improve its security. It is of course important to chose a component that would closely match your interests; given the size of OpenStack, becoming closely familiar with the chosen component's code base, deployment and administration practices might require significant time investments. Once you have chosen a component, send an email on the OSSG email list to let others know about your intentions.
See https://wiki.openstack.org/wiki/Security/How_To_Contribute for more details on how you can improve OpenStack security.
Software Activities
The OpenStack Security SIG has a number of ongoing activities that aim to enhance security of the OpenStack cloud ecosystem. These predominantly break down into three groups; Advisory, Guidance and Software.
Bandit - Python Security Linter
Bandit is a security linter for Python source code, utilizing the ast module from the Python standard library. The ast module is used to convert source code into a parsed tree of Python syntax nodes. Bandit allows users to define custom tests that are performed against those nodes. At the completion of testing, a report is generated that lists security issues identified within the target source code.
Bandit is located under the PyCQA repository on github: https://github.com/PyCQA/bandit
Bandit can also be installed directly via pip: https://pypi.org/project/bandit/
Syntribos - Python API security testing tool
Syntribos is an open source automated API security testing tool that is maintained by members of the OpenStack Security SIG.
Given a simple configuration file and an example HTTP request, syntribos can replace any API URL, URL parameter, HTTP header and request body field with a given set of strings. Syntribos iterates through each position in the request automatically. The tool aims to automatically detect common security defects such as SQL injection, LDAP injection, buffer overflow, etc. In addition, it can be used to help identify new security defects by automated fuzzing.
Syntribos can be installed directly from pypi with pip.
Tatu - SSH certificate and bastion management
Tatu is an OpenStack service that manages SSH user and host certificates. Tatu can also start and manage bastion servers so that you don't have to (and you don't have to give every SSH server a public IPv4 address).
Advisory Activities
The Security SIG issues Security Notes targeted at OpenStack Users and Vendors who either run or package OpenStack for use by downstream consumers.
Security Advisories - OSSA
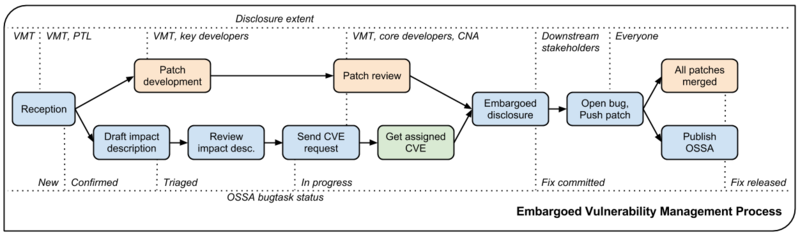
The VMT is a small group of experienced developers who receive, triage and release fixes for vulnerabilities in OpenStack. The final stage of fixing a vulnerability is to release a Security Advisory for the community. The OSSA details the nature of the vulnerability and any workaround or patches required to mitigate it. The Security SIG works closely with the VMT assisting with feedback on various issues.
- Read more about the VMT process on their dedicated webpage
- View the issued OSSA list
Security Notes - OSSN
Security Notes are designed to complement the Security Advisories issued by the Vulnerability Management Team. Security notes can be issued for almost anything affecting the security of potential OpenStack deployments. In many cases a vulnerability may be reported that cannot be fixed immediately because the fix might break the API or otherwise cause service-breaking issues for downstream consumers. Often the Security SIG write notes that will guide deployers in how to best mitigate the issues when an OSSA cannot be provided. OSSNs are also issued for significant vulnerabilities in third party applications that would affect OpenStack deployments.
Guidance Activities
Most of the documentation we produce, be it the security guide or security advisories are focussed on downstream consumers of OpenStack technology. We are also actively working on guidance and tooling for *developers* in the hope that we can help stop vulnerabilities making it into code in the first place.
See the Developer Guideline section of https://security.openstack.org for more info
Security Guide
This book was written by a close community of security experts from the OpenStack Security SIG in a short, intense week-long effort at an undisclosed location. One of the goals for this book is to bring together interested members to capture their collective knowledge and give it back to the OpenStack community.
See http://docs.openstack.org/sec/
Security Blog
We now have a blog, take a look to see the latest of what has been happening in the OpenStack Security world: https://openstack-security.github.io/
Vulnerability Management Team
The OpenStack Vulnerability Management team is the first point of contact for OpenStack security issues. They are responsible for the vulnerability handling and disclosure process.