Difference between revisions of "PolicyGuidedFulfillment"
| Line 25: | Line 25: | ||
** Events/Incident handling: where to aggregate/Process/Notify | ** Events/Incident handling: where to aggregate/Process/Notify | ||
** Remediation: How to fix issues (e.g. Auto-scale – Who decides, What to do; Reaction in production to security threat or compliance issue) | ** Remediation: How to fix issues (e.g. Auto-scale – Who decides, What to do; Reaction in production to security threat or compliance issue) | ||
| + | |||
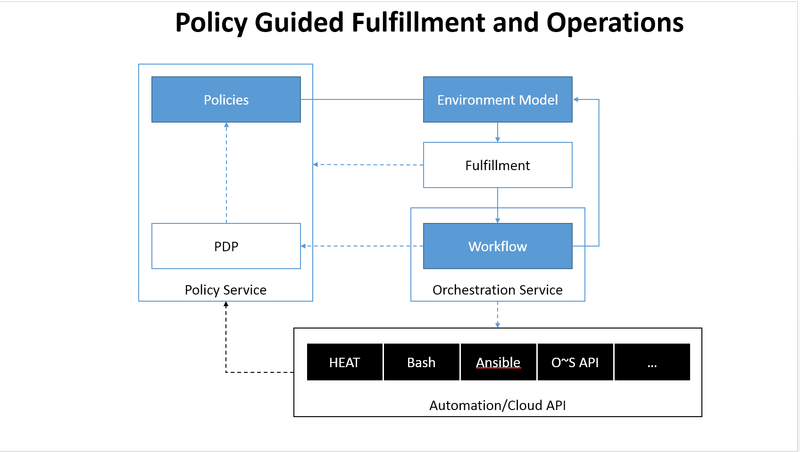
[[File:Overall_model.png|800px|Policy Guided Fulfillment and Operations]] | [[File:Overall_model.png|800px|Policy Guided Fulfillment and Operations]] | ||
| + | |||
| + | |||
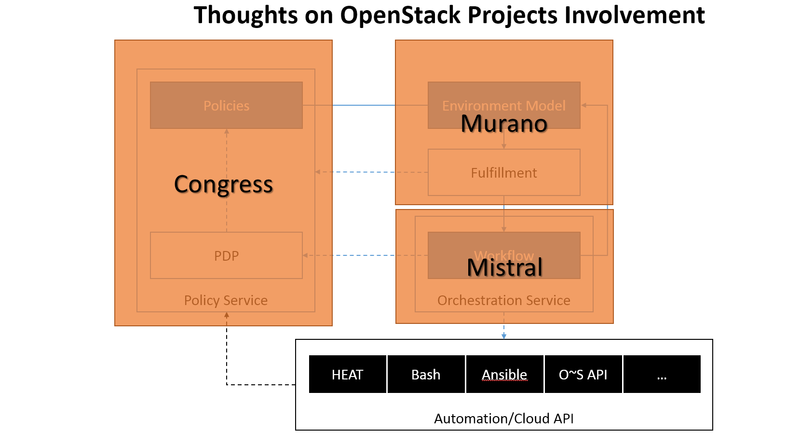
| + | [[File:Projects_thoughts.png|800px|Thoughts on OpenStack Projects Involvement]] | ||
| + | |||
| + | == Next Steps == | ||
| + | |||
| + | * Agreement to support the use cases | ||
| + | * Setup a Coordinated activity across Murano, Congress and Mistral | ||
| + | * Agreed division of roles between projects and technical direction + blueprints | ||
| + | |||
| + | = Background - Possible Technical Approach = | ||
| + | |||
| + | == Proposed Approach == | ||
| + | |||
| + | * Evolve Murano Models to support binding to policies | ||
| + | ** Compatible with existing model approach | ||
| + | * Expand Congress to widen the set of use cases | ||
| + | * Evolve Murano/Mistral to fulfill (Provision then manage) the Environment guided by the policies: | ||
| + | ** Policies can modify model | ||
| + | ** Execution plans are precompiled and impacted by policies | ||
| + | ** Execution plans are executed in mistral by orchestrating: | ||
| + | *** OpenStack APIs | ||
| + | *** HOT/Heat | ||
| + | *** Ansible | ||
| + | *** Python | ||
| + | *** … | ||
| + | * Instances are tracked for subsequent manual or policy driven management | ||
Revision as of 11:24, 4 November 2014
Contents
Business Use Case
- Facilitating reusable policies across workloads:
- Enforcing Policies on Murano Environments Following Company Policies
- Facilitate distribution of Workload across hosts
- Facilitate specification of Monitoring and subsequent remediation (e.g. auto-Scaling)
- Deployment of specific workload in specific security zones
- Customer Examples:
- Desire to use same IT policies on “traditional” and for workload on OpenStack
- DevOps with “Ops” setup added at production without other changes
- Evolution towards Autonomous IT beyond just Auto-Scaling
Objectives
- Add ability to use policies to guide provisioning workloads and their subsequent management:
- Declaratively attached to models
- Separation of concern from development (e.g. can change across stages)
- Examples of Use Cases:
- Provisioning: Select how to best provision among options
- E.g. Placement (location, security zone, Staging zone) choices; Requirements on infrastructure
- Monitoring: Setup OpenStack or external systems to monitor the workload / Environment:
- Performance/Ops
- Security
- Usage
- Compliance
- Events/Incident handling: where to aggregate/Process/Notify
- Remediation: How to fix issues (e.g. Auto-scale – Who decides, What to do; Reaction in production to security threat or compliance issue)
- Provisioning: Select how to best provision among options
Next Steps
- Agreement to support the use cases
- Setup a Coordinated activity across Murano, Congress and Mistral
- Agreed division of roles between projects and technical direction + blueprints
Background - Possible Technical Approach
Proposed Approach
- Evolve Murano Models to support binding to policies
- Compatible with existing model approach
- Expand Congress to widen the set of use cases
- Evolve Murano/Mistral to fulfill (Provision then manage) the Environment guided by the policies:
- Policies can modify model
- Execution plans are precompiled and impacted by policies
- Execution plans are executed in mistral by orchestrating:
- OpenStack APIs
- HOT/Heat
- Ansible
- Python
- …
- Instances are tracked for subsequent manual or policy driven management