Difference between revisions of "Horizon/DomainWorkFlow"
(→Cloud Admin account in keystone) |
Dan Nguyen (talk | contribs) |
||
| (10 intermediate revisions by 3 users not shown) | |||
| Line 12: | Line 12: | ||
grep -i 'admin_token' /etc/keystone/keystone.conf | grep -i 'admin_token' /etc/keystone/keystone.conf | ||
* Grant the admin access to the cloud admin domain | * Grant the admin access to the cloud admin domain | ||
| − | curl -s -H "X-Auth-Token: < | + | curl -s -H "X-Auth-Token: <ADMIN_TOKEN>" -X PUT http://127.0.0.1:5000/v3/domains/default/users/<ADMIN_ID>/roles/<ADMIN_ROLE_ID> |
| + | Note: If you are having trouble finding the ADMIN_ID, you can find it with this command: | ||
| + | mysql -D keystone -e 'select id from user where name = "admin";' | ||
| + | Note: If you are having trouble finding the ADMIN_ROLE_ID, you can find it with this command: | ||
| + | mysql -D keystone -e 'select id from role where name = "admin";' | ||
==== keystone policy.json file==== | ==== keystone policy.json file==== | ||
| Line 19: | Line 23: | ||
Change the following line in the policy.v3cloudsample.json and swap it with the /etc/keystone/policy.json | Change the following line in the policy.v3cloudsample.json and swap it with the /etc/keystone/policy.json | ||
| + | Remember: He who laughs last had a backup! | ||
| + | |||
| + | old: | ||
... | ... | ||
"cloud_admin": "rule:admin_required and domain_id:admin_domain_id", | "cloud_admin": "rule:admin_required and domain_id:admin_domain_id", | ||
... | ... | ||
| − | + | new: | |
... | ... | ||
# use 'default' or whatever your cloud admin domain id is | # use 'default' or whatever your cloud admin domain id is | ||
| Line 49: | Line 56: | ||
==== keystone v3 ==== | ==== keystone v3 ==== | ||
Horizon needs to be configured to use keystone v3 and multi domain support | Horizon needs to be configured to use keystone v3 and multi domain support | ||
| + | |||
| + | Copy the keystone devstack's policy file: /etc/keyston/policy.json into your horizon directory: | ||
| + | horizon/openstack_dashboard/conf/keystone_policy.v3cloudsample.json | ||
| + | |||
| + | Determine the default role name: | ||
| + | mysql -D keystone -e 'select name from role where name like "%ember";' | ||
| + | In my case it has changed from "_member_" to "Member". | ||
| + | |||
local_settings.py | local_settings.py | ||
| + | ... | ||
| + | OPENSTACK_KEYSTONE_DEFAULT_ROLE = "Member" | ||
... | ... | ||
OPENSTACK_API_VERSIONS = { "identity": 3, } | OPENSTACK_API_VERSIONS = { "identity": 3, } | ||
OPENSTACK_KEYSTONE_MULTIDOMAIN_SUPPORT = True | OPENSTACK_KEYSTONE_MULTIDOMAIN_SUPPORT = True | ||
| + | OPENSTACK_KEYSTONE_DEFAULT_DOMAIN = 'default' | ||
OPENSTACK_KEYSTONE_URL = "http://%s:5000/v3" % OPENSTACK_HOST | OPENSTACK_KEYSTONE_URL = "http://%s:5000/v3" % OPENSTACK_HOST | ||
| + | ... | ||
| + | POLICY_FILES = { | ||
| + | #'identity': 'keystone_policy.json', | ||
| + | 'identity': 'keystone_policy.v3cloudsample.json', | ||
... | ... | ||
| Line 61: | Line 83: | ||
https://review.openstack.org/#/c/141153/ | https://review.openstack.org/#/c/141153/ | ||
| + | ==== horizon ==== | ||
| + | You'll need to pull down this patch in your horizon repo for horizon to understand multi-domain setups. | ||
| + | https://review.openstack.org/#/c/148082/ | ||
| + | |||
| + | ==== keystone ==== | ||
| + | Allows a Domain Admin to list role assignments without a project token | ||
| + | https://review.openstack.org/#/c/180846/ | ||
| + | |||
| + | ==== keystone client ==== | ||
| + | Allows a Domain Admin to list role assignments without a project token | ||
| + | https://review.openstack.org/#/c/188184/ | ||
=== Users === | === Users === | ||
| Line 68: | Line 101: | ||
* Domain Admin | * Domain Admin | ||
* User (_member_ role) | * User (_member_ role) | ||
| + | |||
| + | ==== Set up the cloud admin user ==== | ||
| + | * Convert the admin user to be a Cloud Admin | ||
| + | curl -s -H "X-Auth-Token: <ADMN_TOKEN>" -X PUT http://127.0.0.1:5000/v3/domains/<DEFAULT DOMAIN>/users/<ADMIN USER ID>/roles/<ADMIN ROLE ID> | ||
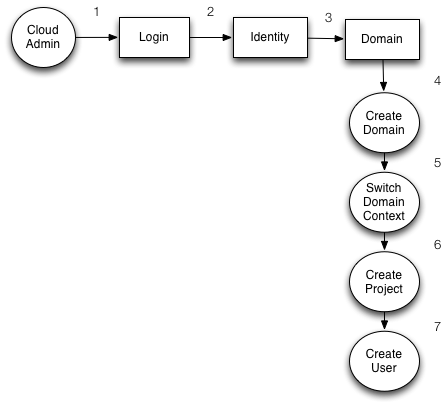
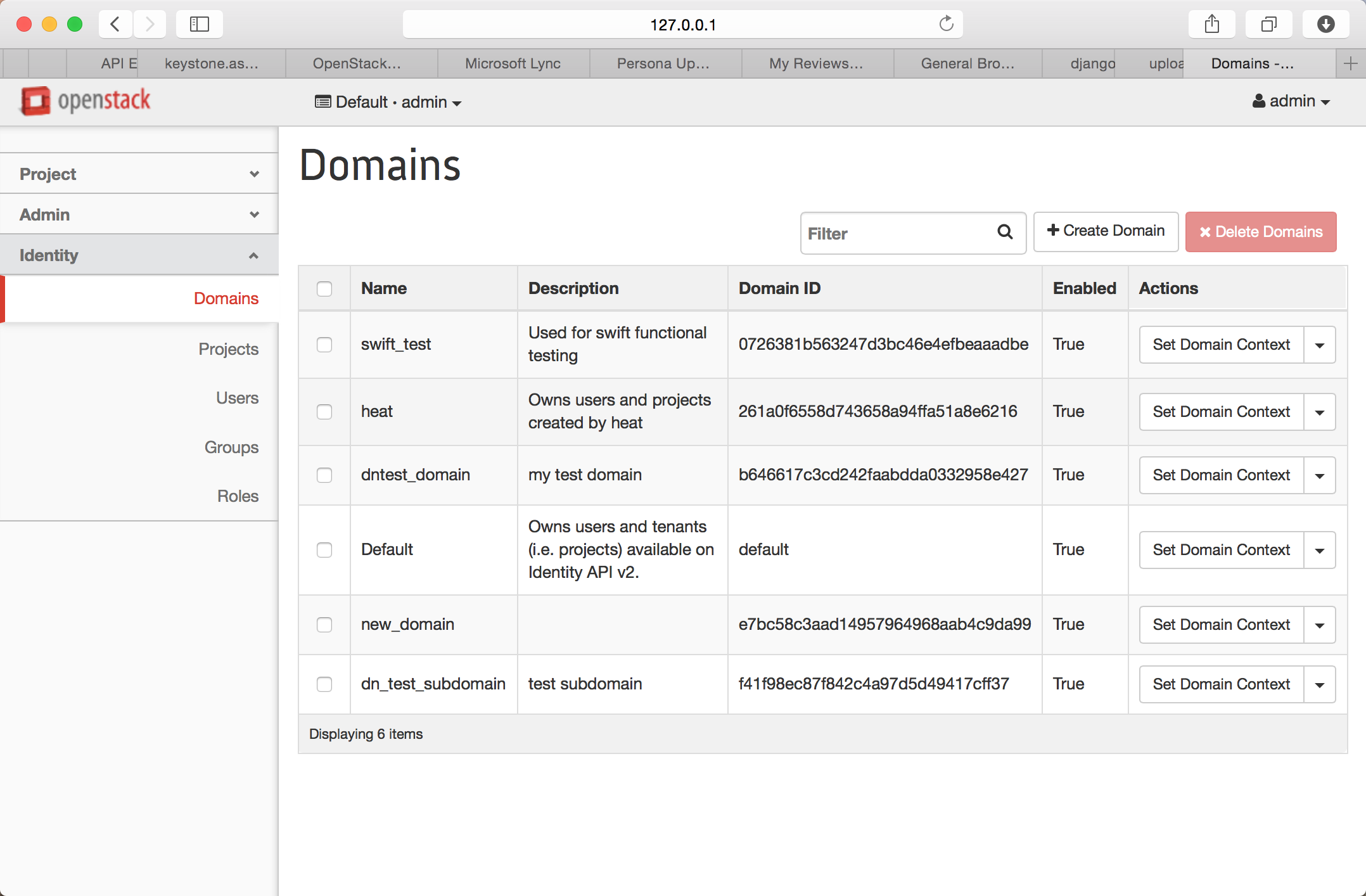
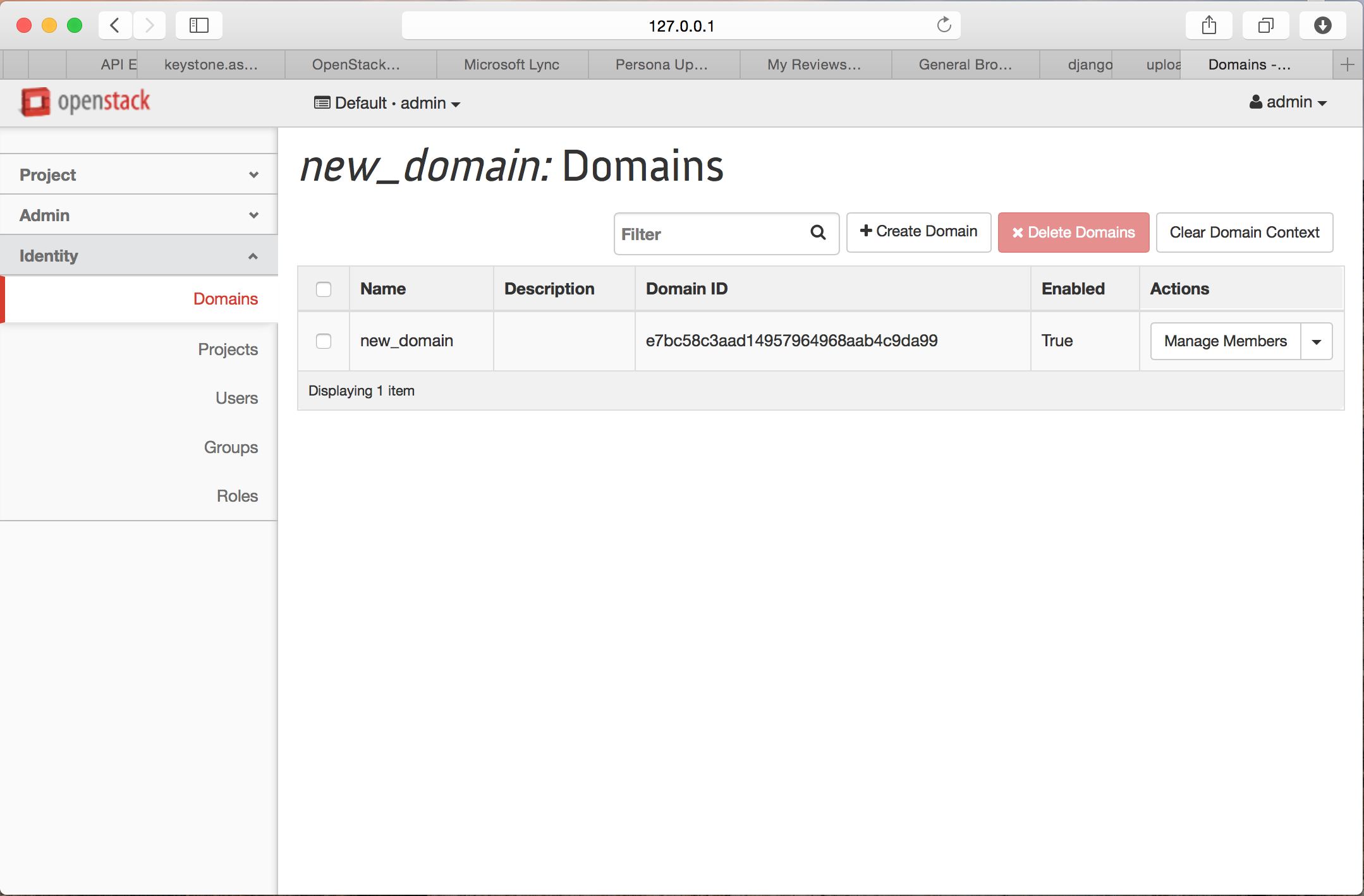
=== Workflow 1. Cloud Admin sets a Domain Context === | === Workflow 1. Cloud Admin sets a Domain Context === | ||
Latest revision as of 19:40, 14 July 2015
Intro
This wiki describes how to enable Domain Scoped Token support in Horizon and how to navigate the existing work flows.
Prerequisites
devstack
You'll need to have keystone running in a VM or somewhere you can reach it from Horizon.
Cloud Admin account in keystone
If a user has an 'admin' role and access to the Cloud Admin domain then they are considered to be a Cloud Admin. One way to enable this account to grant your admin user access to the 'default' domain.
- Dig the admin token out of keystone.conf
grep -i 'admin_token' /etc/keystone/keystone.conf
- Grant the admin access to the cloud admin domain
curl -s -H "X-Auth-Token: <ADMIN_TOKEN>" -X PUT http://127.0.0.1:5000/v3/domains/default/users/<ADMIN_ID>/roles/<ADMIN_ROLE_ID>
Note: If you are having trouble finding the ADMIN_ID, you can find it with this command:
mysql -D keystone -e 'select id from user where name = "admin";'
Note: If you are having trouble finding the ADMIN_ROLE_ID, you can find it with this command:
mysql -D keystone -e 'select id from role where name = "admin";'
keystone policy.json file
You can start testing with the default /etc/keystone/policy.json file but at some point you will want to switch in the following file: https://github.com/openstack/keystone/blob/master/etc/policy.v3cloudsample.json
Change the following line in the policy.v3cloudsample.json and swap it with the /etc/keystone/policy.json Remember: He who laughs last had a backup!
old:
... "cloud_admin": "rule:admin_required and domain_id:admin_domain_id", ...
new:
... # use 'default' or whatever your cloud admin domain id is "cloud_admin": "rule:admin_required and domain_id:default", ...
memcached
- Memcached should be installed and running (perhaps on the same host as horizon to keep things simple)
- The memcached client library needs to be installed in horizon's venv (python-memcached==1.53)
- Horizon needs to be configured to use memcached
local_settings.py
...
# We recommend you use memcached for development; otherwise after every reload
# of the django development server, you will have to login again. To use
# memcached set CACHES to something like
CACHES = {
'default': {
'BACKEND': 'django.core.cache.backends.memcached.MemcachedCache',
'LOCATION': '127.0.0.1:11211',
}
}
SESSION_ENGINE = 'django.contrib.sessions.backends.cache'
...
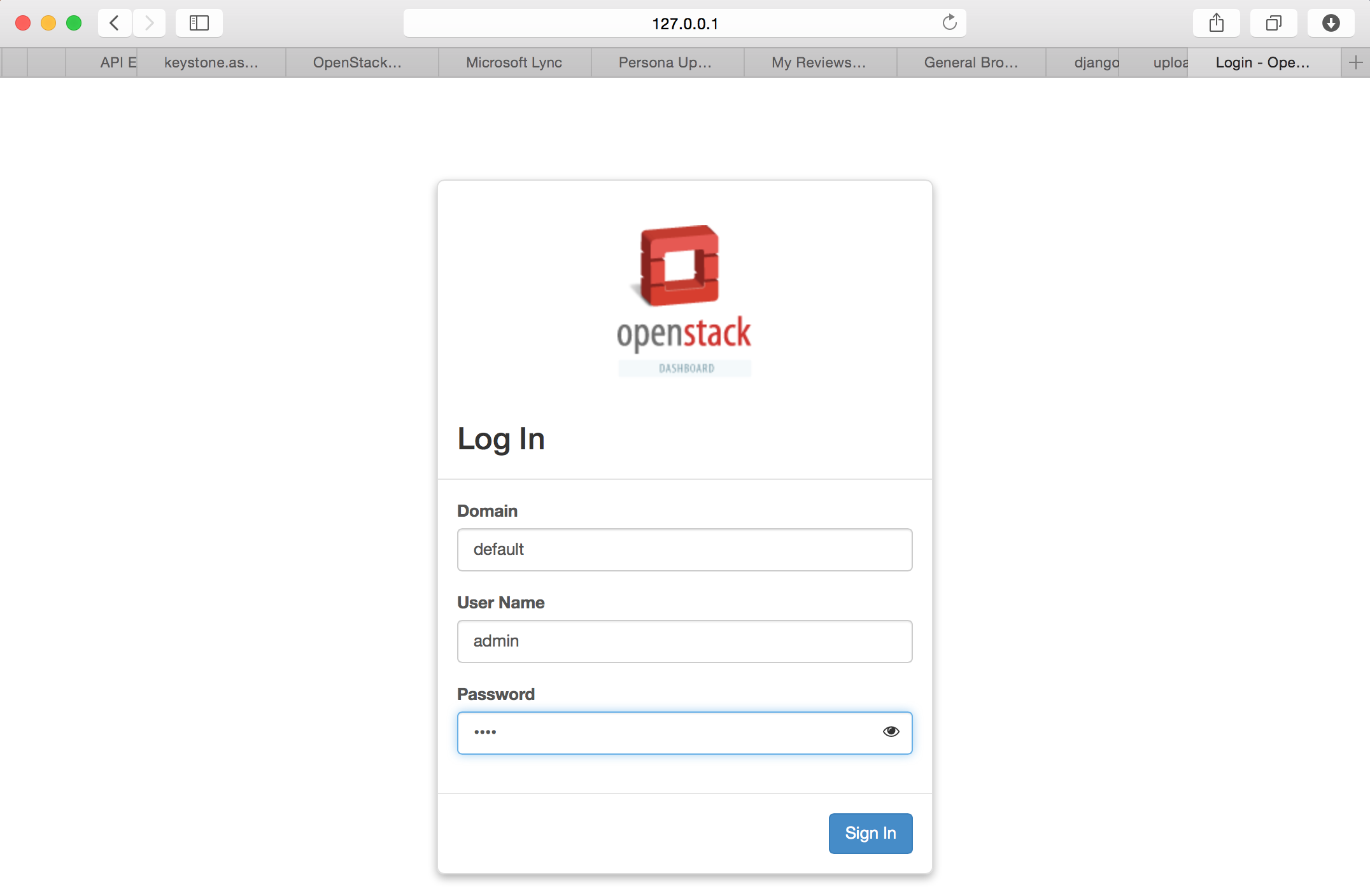
keystone v3
Horizon needs to be configured to use keystone v3 and multi domain support
Copy the keystone devstack's policy file: /etc/keyston/policy.json into your horizon directory: horizon/openstack_dashboard/conf/keystone_policy.v3cloudsample.json
Determine the default role name:
mysql -D keystone -e 'select name from role where name like "%ember";'
In my case it has changed from "_member_" to "Member".
local_settings.py
...
OPENSTACK_KEYSTONE_DEFAULT_ROLE = "Member"
...
OPENSTACK_API_VERSIONS = { "identity": 3, }
OPENSTACK_KEYSTONE_MULTIDOMAIN_SUPPORT = True
OPENSTACK_KEYSTONE_DEFAULT_DOMAIN = 'default'
OPENSTACK_KEYSTONE_URL = "http://%s:5000/v3" % OPENSTACK_HOST
...
POLICY_FILES = {
#'identity': 'keystone_policy.json',
'identity': 'keystone_policy.v3cloudsample.json',
...
django-openstack-auth
You'll need to pull down this patch to be able to retrieve a domain scoped token from the http session. https://review.openstack.org/#/c/141153/
horizon
You'll need to pull down this patch in your horizon repo for horizon to understand multi-domain setups. https://review.openstack.org/#/c/148082/
keystone
Allows a Domain Admin to list role assignments without a project token https://review.openstack.org/#/c/180846/
keystone client
Allows a Domain Admin to list role assignments without a project token https://review.openstack.org/#/c/188184/
Users
This page only considers three users
TODO(esp): Add use cases for Cloud Admin and Domain Admin
- Cloud Admin
- Domain Admin
- User (_member_ role)
Set up the cloud admin user
- Convert the admin user to be a Cloud Admin
curl -s -H "X-Auth-Token: <ADMN_TOKEN>" -X PUT http://127.0.0.1:5000/v3/domains/<DEFAULT DOMAIN>/users/<ADMIN USER ID>/roles/<ADMIN ROLE ID>