Barbican/Blueprints/dogtag-plugin
< Barbican | Blueprints
- Launchpad Entry: https://blueprints.launchpad.net/barbican/+spec/dogtag-plugin
- Created: 16-Jan-2014
- Updated: 31-Mar-2014
- Contributors: John Wood, Chad Lung, Doug Mendizabal, Lisa Clark, Sheena Gregson, Ade Lee, Endi Dewata
Abstract
This blueprint is for creating a Barbican crypto plugin so that Barbican deployments can use the RedHat DogTag Data Recovery Manager (DRM) as a key management back-end.
Description
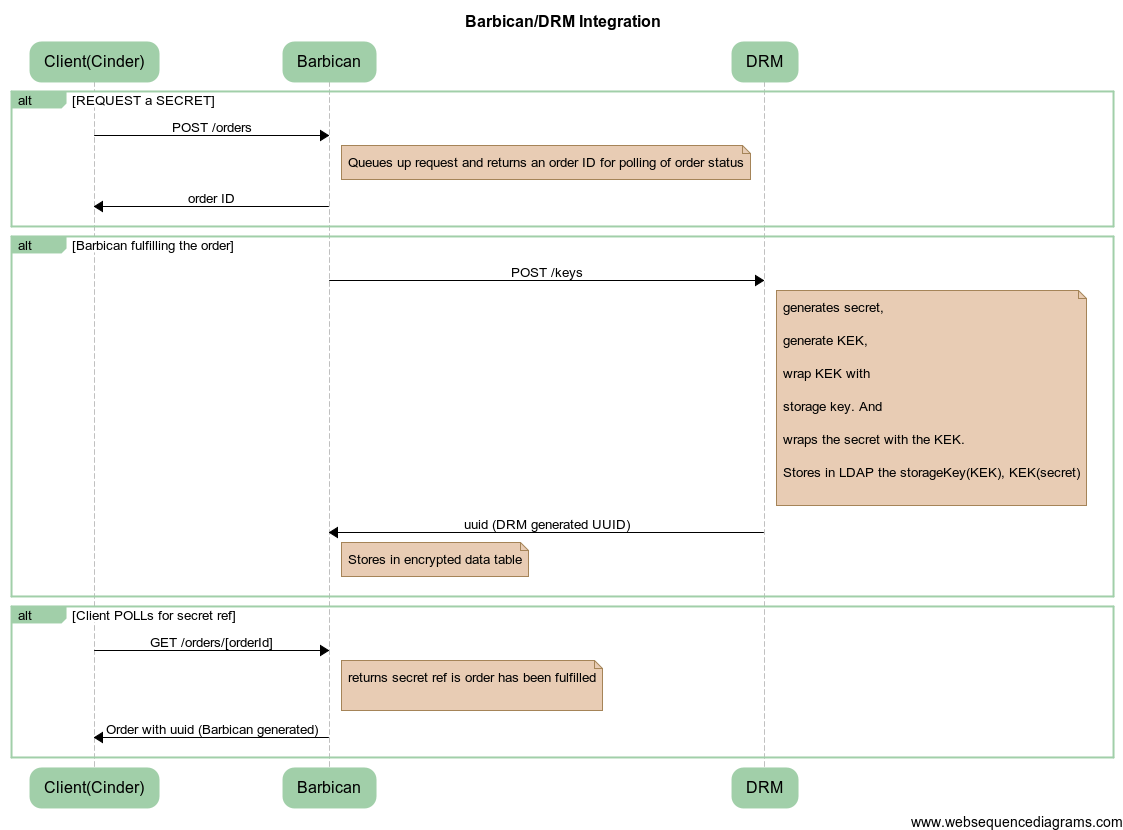
To support a RedHat DRM as a key management back-end, changes will be needed relative to 2 main workflows:
Creating a secret
- NOTE: Between Barbican and DRM will be the DogTag plugin to integrate with DRM.
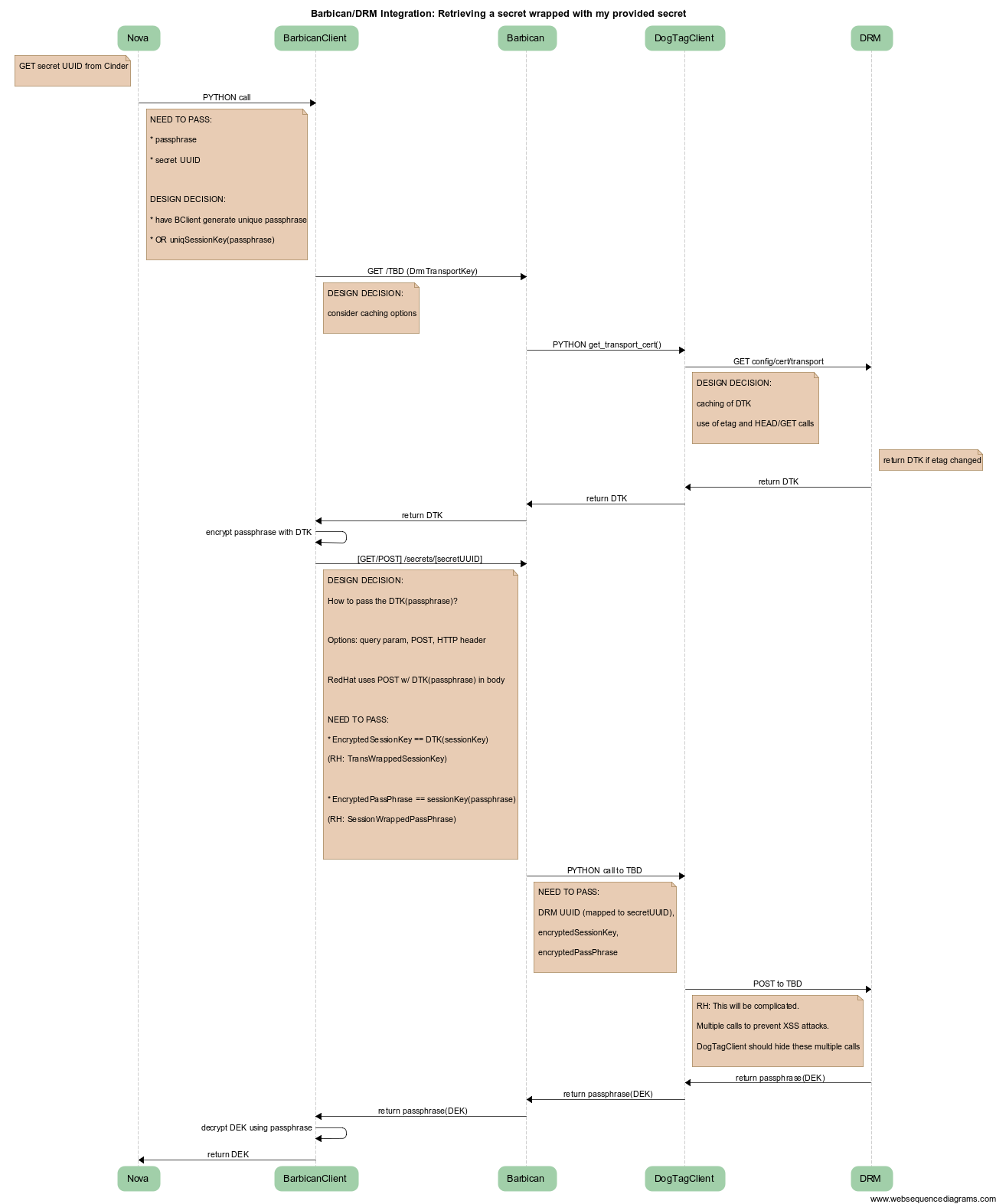
Retrieving a secret
Proposed Changes
- python-barbicanclient
- Modify to support retrieving a transport key for encryption and decryption between Barbican client and Barbican
- Generate a session key for the lifespan of the transaction to encrypt data sent and decrypt data received
- Allow clients to optionally provide a passphrase, else self generate.
- Decrypt the retrieved secret using the session encrypted passphrase.
- Barbican
- API
- New resource to retrieve a transport key and to use the crypto plugin to retrieve a transport key
- Initial setup: During installation of a DogTag DRM, a user and certificate is created and the public cert is available for use in Barbican
- Config changes to support configuration specific to DogTag Plugin
- Crypto Plugin interface
- modify create() method to return the encrypted datum (vs the current raw data). It should have the same return contract as the encrypt() method (i.e. the secret generation and the secret encryption operations will be combined).
- new method() to return a transport key
- Dev Plugin
- Modify to support different contract behavior on create()
- DogTag Crypto Plugin
- abstraction layer for the DogTag Python library
References
[1] Blueprint
[3] Python Barbican Client on Github
[4] RedHat DogTag
[5] DogTag REST